The WannaCry ransomware attack was unleashed a year ago. In the UK, it had a particular impact on the NHS, and its lessons and implications have been extensively studied. Lyn Whitfield looks back.
Flashback: the WannaCry attack
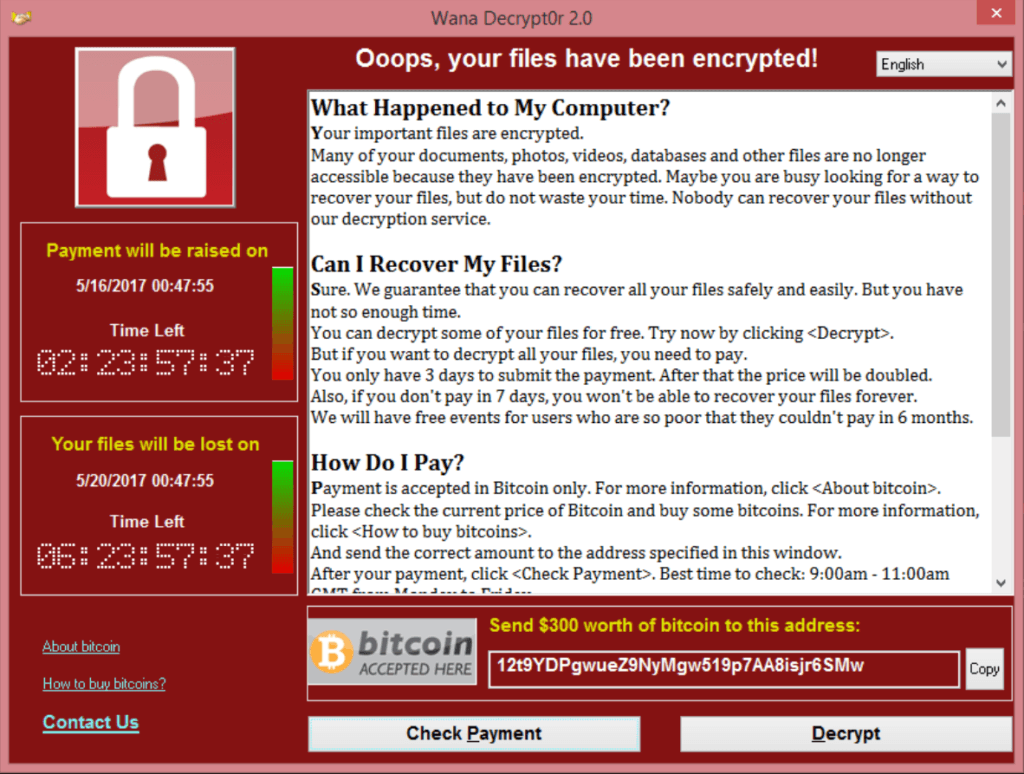
The WannaCry ransomware attack was launched early on 12 May 2017. It locked users out of computers running Windows and demanded a ransom in the crypto currency, Bitcoin.
WannaCry spread through an exploit called EternalBlue, which may have been developed by the US National Security Agency. In April, it was leaked by a hacker group called Shadow Brokers.
The previous month, Microsoft had issued a patch for all the versions of Windows that it was supporting at the time (ie Windows 7 and up). Despite this, WannaCry was able to affect 200,000 computers across 150 countries, before it was stopped by a kill-switch discovered by @malwaretechblog (Marcus Hutchins).
In the UK, the NHS was particularly badly affected, with around 70,000 devices infected. At the time, its continued use of the older Windows XP operating system was suggested as a reason for this.
However, a subsequent study by Kaspersky Lab estimated that only 0.1% of the global computers infected were running XP, which tended to crash before it could load WannaCry. Around 98% of the affected computers were running Windows 7.
By mid-June, it was reported that 327 payments worth $130,000 were made in response to WannaCry infection, which security companies pinned on a hacking group called Lazarus or Hidden Cobra.
The group has also been blamed for bank-heists and attacks on South Korean companies, and in December the US and related governments blamed North Korea for the attack. North Korea has denied this.
WannaCry and the NHS
Reports that hospitals were being affected by WannaCry were starting to appear on websites and social media by lunchtime on 12 May. Initially, it looked as if around 16 organisations were affected, with some prominent trusts – such as Barts Health in London – asking patients to avoid A&E and use other services if possible.
Other services were disrupted as organisations shut down their networks – the NHS in Wales blocked all external emails as it patched national and local systems. Most trusts had recovered by the start of the following week – although Barts, which took longer, estimated that it lost £9.5 million in income and £4.8 million calling in IT support.
NHS England, which had declared a “major incident” at 4pm on 12 May, formally stood it down at 5.30pm on 19 May. Since then, the impact, lessons and legacy of WannaCry have been closely studied:
National Audit Office:
The national spending watchdog issued its report ‘Investigation: WannaCry cyber-attack and the NHS’ in October 2017.
The report put a firm figure on the number of organisations affected: 81 out of 236 trusts in England were infected or switched off their systems to avoid infection, and 603 primary care organisations were infected.
It was also highly critical of the NHS’ state of readiness for what it described as “a relatively unsophisticated attack”. It pointed out that the National Data Guardian and the Care Quality Commission had published reports on data security in July 2016; but the Department of Health took a year to respond.
In the meantime, neither the department nor its arms-length bodies knew how prepared local organisations were (or weren’t). Specifically, its report said: “In March and April 2017, NHS Digital had issued critical alerts warning organisations to patch their systems to prevent WannaCry. However, the Department had no formal mechanism for assessing whether NHS organisations had complied with its advice and guidance.”
Once WannaCry hit, the NAO added, there was no rehearsed plan to co-ordinate a response, and no means of communicating with trusts that were infected or that had shut down their email; local staff used mobiles and WhatsApp to communicate with each other.
Despite this, the watchdog accepted the NHS was trying to learn lessons. Four months on, it said NHS England and NHS Improvement had written to boards “asking them to ensure” they had implemented CareCERT alerts, and were in the process of drawing up new response and communications plans.
NHS Digital:
NHS England’s IT agency issued its own ‘Lessons learned review of the WannaCry Ransomware Cyber Attack’ in February 2018.
Apparently stung by the NAO report, chief information officer Will Smart argued that the NHS had “responded well to what was an unprecedented incident” and thanked NHS staff “for their resilience and extraordinary efforts in going the extra mile to keep… services running for patients.”
He also outlined some of the immediate measures that had been taken to respond, including: on-site cyber security assessments at 190 trusts; the release of £21 million of capital funding to strengthen major trauma centres; the release of a further £25 million to implement high-severity CareCERT alerts at trusts that hadn’t implemented them; and a new portal to monitor compliance.
Also: the creation of a 24/7 data security hotline; a procurement for a new security operations centre; more online advice for trusts; an updated Information Governance Toolkit; and various measures to improve communications, including “text alerts to NHS chief executives and CIOs when email is unavailable.”
Even so, the lessons learned document warned, “it is not a question of ‘if’ but ‘when’ the next cyber-attack occurs”, so NHS England and NHS Digital should formalise their roles and responsibilities for when it hits.
Also, that trusts should: review their IT and cyber security capacity; aim to meet all relevant standards; improve their management of systems and devices; review business continuity plans; train staff for potentially “long-running and intense” attacks; and remember the need to support primary and social care.
Public Accounts Committee:
The National Audit Office reports to the Public Accounts Committee, which then holds hearings on its findings, and publishes its views. MPs issued a report on the ‘Cyber-attack on the NHS’ in April, and concluded it had been “lucky” that it had not been worse.
“If the attack had not happened on a Friday afternoon in the summer, and the kill switch to stop the virus had not be found relatively quickly, the disruption could have been much worse,” it said. After re-iterating the NAO view that the NHS had been “unprepared” for the attack, and that it had been pushed into using “improvised and haphazard ways to communicate”, the report focused on the future.
It pointed out that the NHS “still does not know what financial impact the WannaCry had on the NHS”, or what it would cost to properly sort out its cyber-security. So, although £50 million has been spent on emergency work, and another £150 million will be diverted to resilience and response in 2018-19 and 2019-20, it doesn’t really know if this money is being well spent.
Also, it argued, the NHS does not have a detailed plan to implement its ‘lessons learned’ report; and that NHS Digital and trusts may lack the staff and skills to do this in a complex environment in which it can be difficult to patch one system without knocking over others.
The PAC recommended: national guidance on how systems can be updated while minimising disruption to services; accreditation for IT and medical systems suppliers; and the creation of workforce plans that focus on IT and cyber security skills.
It also said it wanted an update on the costs of WannaCry to the NHS, and a breakdown of how national and local bodies will target investment “in line with service and financial risks” – by June.